My Bug Bounty Journey & Ranking 1st in U.S. DoD & Achieving top 100 hackers in 1 year

Hello,
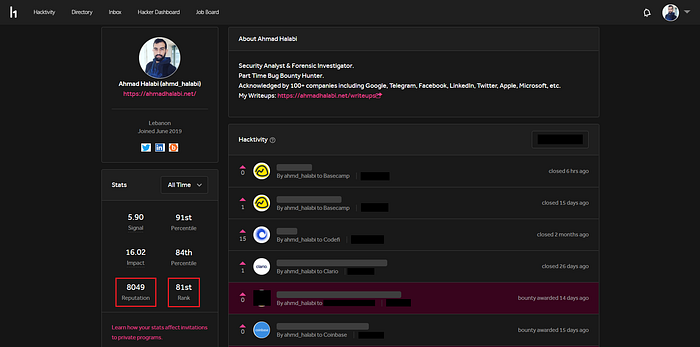
My name is Ahmad Halabi. A lot of people are asking me how I reached top 100 hackers scoring over 8k reputation on hackerone in a very short time (1 year and 4 months) and how I reached 1st rank in U.S. DoD. I am also receiving lots of questions about how to start in bug bounty hunting, what is my methodology that I use, and so many other related questions. So I decided to write an article talking about my journey in bug bounty, how I reached where I am now in short time, and how you can make great achievements as well.
So let’s start !
Introduction ::
First of all, you will be surprised that I was very late when I knew about technology and computers in general, back in 2016 when was the first time I had a mobile phone and internet connection. I knew about hacking in general in 2016, what excited me to learn hacking is when my laptop was hacked in 2017 so I felt curious to know how it happened. Due to the high school I wasn’t able to learn hacking, So I kept it as a general hobby until I finished. Then I started University studying Computer Science Major and during that time, I started to learn hacking.
In February 2019, I heard about bug bounties from a security researcher named Jafar Abu Nada who found a bug in Eset and put his PoC on his youtube channel, We became friends after that :) , I didn’t know anything about bug bounties so I started searching about what is it. I admit that I started learning bug bounty hunting in the wrong way, because I didn’t have enough resources and I didn’t know where and how to start.
Finding my first valid bugs ::
After struggling and searching, I learned couple of simple bugs. Then I directly rushed to the companies that offer vulnerability disclosure program. I remember that the first bug I found is in February 2019 where it was `Clickjacking` in `Panda Security` and they awarded me a certificate of appreciation, I was so happy. In the same month I also found the same valid bug in `360 Security` and I also got listed in their hall of fame. I was so excited because I started knowing how things work.
I kept searching for low valid bugs like clickjacking and session managements for 4 months from February till June. During these 4 months, I was lucky to find an RCE via file upload in blackberry with my simple beginner knowledge and got listed in their hall of fame. Since there, clickjacking was my favorite bug 😂.
In June 2019, I knew about hackerone and bugcrowd platforms. I was excited to create account and start hacking. And here I got very disappointed because of getting a lot of duplicates and N/A bugs. I hated bug bounty. My reputation decreased to 67 I think with signal <-3. I decided to quit for a while and search and learn a lot until I find a way to raise my reputation and signal and submit valid reports.
Getting a real start in bug hunting ::
Even when I decided to search and learn, I was doing it the wrong way. Haha I will not state how I was learning and testing for bugs because you will absolutely laugh about how I was very beginner 😂.
You can say that in July 2019, I started knowing how to learn bug hunting the right way.
- I watched
Frans Rosen& hackeronetalks about bug bounty hunting. - I searched Google and Youtube about videos that gives you hints on how to start bug bounty hunting.
- I collected bugcrowd and hackerone vulnerability titles and types when submitting a bug and started googling every vulnerability type and learn what is it and how to exploit it.
Still I didn’t learn it the best way but it was enough for me to understand what is bug bounty, how to get started and find bugs.
After that I found that it is time to deploy what I learned on real environments, So after searching I chose U. S. Department Of Defense program on hackerone to apply what I learned on its domains.
Achieving 1st Rank in U.S. Dept Of Defense (2019) ::
Through performing this cycle loop (Learn & Apply) on DoD domains, I found myself ranked 1st in their program for the year 2019. To be honest I expected that because I was working very hard to learn a lot and doing it in the smart way.

So, still the question, How I reached 1st rank in DoD ?
I admit that I am smart in Tech field. I just needed to know how to begin and to know some hints, and when I knew good info about that, I was able to start my real hacking on hackerone.
From July 2019 till the end of Dec 2019 I gathered around 2.8k reputation on hackerone.
What I was talking about being smart, here are hints on how I found a lot of bugs in DoD :
- DoD runs huge number of domains and subdomains.
- DoD accepts 1 bug type per 1 subdomain. So if you find 1 special bug in multiple subdomains, you will get it valid on all those subdomains.
- I found an information disclosure bug that was found in many subdomains. So I automated its finding process and reported it and got reputation.
- Then I found a bypass for the previous bug and I also automated its finding process and got reputation.
- Most bug types that I found in DoD were: Information Disclosure, XSS, IDOR, RCE, DOS, CSRF, Business Logic Bugs and Violation of secure design principle.
Note that in 2019, I was not seeking for bounties. I just got 2 bounties in the whole year, one from Facebook and the other one from Telegram.
You will see above that it was not so hard for me to achieve 1st rank in U.S. DoD, it required to be smart, real studying and persistent hacking.
Getting on the right learning path ::
At the beginning of 2020 and after a lot of searching, I started the right learning path. So I started to read writeups, PoC’s, learn new hacking techniques and join the bug bounty community.
From January 2020 till June 2020, I still wasn’t getting good bounties because I was still focusing on increasing my knowledge and becoming a better version of myself as a hacker.
In July 2020, I started focusing on increasing vulnerability impacts and getting good bounty amount in addition to continuous learning.
Achieving top 100 hackers in 1 year & 4 months ::
In October 2020, I reached over 8k reputation and I became Top 100 hackers ranking 81st among hackers worldwide in hackerone. Which is something I am really proud of.
I stopped hacking on VDP (Ineligible) programs and I am currently hacking on VRP (Eligible) programs.
I am currently a part time bug bounty hunter. I don’t spend specific amount of hours hunting, it depends, sometimes I spend 2 hours, sometimes 6 hours. It depends on the mood and productivity.
And my advice for all newbies: don’t hack for money, focus on learning and reaching a good level in bug hunting then after that go focus on earning as much as you want. That what I did and look where I am now (all thanks goes to God).
This part is where you want to reach 😅 and it is the most important part for people who are asking me how to start in bug bounties and what is the methodology that I use.
Start Learning Bug Bounty Hunting ::
In order to be successful in bug bounty hunting, you need to know what is penetration testing especially web application penetration testing. Once you get enough information in web app pentesting, you can go for mobile app pentesting as well and enlarge your knowledge in all the fields related to Penetration Testing.
Here I will just focus on Learning web application penetration testing.
Note that I didn’t follow this learning process because as I mentioned previously, I faced many problems on how to start and whom to follow and learn from. But according to my experience after I learned enough, I believe that the great resources that I will provide below will absolutely enlarge your penetration testing knowledge and makes you get better in this field.
- Learn web application penetration testing techniques from PortSwigger Web Security Academy (https://portswigger.net/web-security).
PortSwigger Academy is an amazing source to start your learning journey with great knowledge and deep understanding of how web application works, how vulnerabilities arise and how to exploit and mitigate them. - Learn Web Application Penetration Testing course from Ebrahim Hegazy (https://www.youtube.com/playlist?list=PLv7cogHXoVhXvHPzIl1dWtBiYUAL8baHj).
This course is delivered by an amazing person, and it will help you understand web app pentesting concept and techniques. It will also help those whose English is not so good because the instructor is speaking in Arabic. - Learn how to start finding bugs from InsiderPhd (https://www.youtube.com/channel/UCPiN9NPjIer8Do9gUFxKv7A).
Katie always deliver great stuff when it comes to finding vulnerabilities in bug bounty programs. You will know how to apply what you learned practically with Katie. - Watch Nahamsec Live Recon Interviews (https://www.youtube.com/channel/UCCZDt7MuC3Hzs6IH4xODLBw).
This will give you a lot of ideas and thoughts of how other hackers think when they approach a target program or when they do bug bounty hunting in general. - Don’t always depend on others. If you came across a vulnerability type that you don’t know, lets say HTTP Request Smuggling for example, go to Google and search about it, how to exploit it, real case scenarios where the bug was found. Be creative and smart.
Writeups Reading is Power !
In addition to the learning resources that I previously mentioned. I highly suggest (must) read writeups, reports and PoCs as much as you can while learning. Because reading writeups enlarges your thinking, increases your perception, and provides you with new ideas to find more and more vulnerabilities.
Below I will mention the top recourses for reading writeups which I personally read from :
- Pentesterland (https://pentester.land/list-of-bug-bounty-writeups.html)
- Hacktivity (https://hackerone.com/hacktivity)
- Bugreader (https://bugreader.com/reports)
- BugBountyWriteups (https://medium.com/bugbountywriteup)
Follow Bug bounty community on Twitter ::
Twitter is valuable platform to follow amazing security researchers in bug bounty field. So I suggest to make a look on Twitter and follow what you think that you can benefit from.
Create your own Methodology ::
You should understand something which is that no one will give you his pure and clear methodology. You must create your own one. What you can do is that you can gather lots of information about this field and use them to end up creating your own methodology which will you use in your hunting journey.
Since a lot of people asked me how I test for bugs, what methodology I use and how I find vulnerabilities so I am going to share with you some of my main points that I stick with while doing bug hunting.
Some of my Methodology that I follow ::
- Since I have Development background, as a quick recon, I created a bash script that automate the subdomain enumeration, live subdomains checking and directory bruteforce process.
- I don’t rely on one single tool, that’s why I also use bash script to run multiple subdomain enumeration tools for example using a single command and output the results in a single file.
- I always keep an eye on burp history and target, sometimes I get simple bug with high impact just because there is a config file exposed having secret tokens inside it which I found while looking in burp history.
- I always take notes about everything interesting that I found. Maybe later I use it or chain it with a bug I found.
- I test as many as target application functionalities and features. May be you will find a broken nonworking feature. (As a real scenario example, I found a broken Connect with Google feature in a public program on hackerone while I was going to test the same feature for IDOR/CSRF. Simply I reported it, represented the impact and got 500 bucks for it).
My advices and Recommendations
- Be professional when writing reports.
- Expect that your bugs may be duplicate or that you will not find any bug at all. First it will be disappointing but then you will find it normal as I do.
- I strongly advice to learn how to automate stuff the easy way without getting too deep if you are not familiar in programming.
- I suggest to learn some programming languages like python & bash for automation and writing scripts, and PHP & JavaScript for understanding how web app works.
- Recon is power, try to find as much information as you can about the target application. From subdomain enumeration, to directory bruteforce, hidden parameters, finding hidden endpoints, fuzzing the target application, playing with all of its functionalities, google dorking, github dorking, and don’t miss checking js files as well.
- Try to bypass the fixes.
- Do it the smart way.
- Think outside the box.
- Don’t overthink.
- Think as a developer when approaching an application. It will help you find more business logical bugs.
- Ask yourself what would be the impact of the bug that you found.
- Don’t seek for bounty, seek for knowledge. Bounty will automatically come and increase according to your knowledge and professionalism.
- Be patient, curious for any knew techniques, inspired.
- Don’t expect good talk from people about you. Do what you believe is right.
- Accept advices from others.
- Work Smart not Hard.
- Believe in yourself and see that all great hackers where beginners just like you in the first.
- Be yourself, create your own path and methodology and do not imitate others.
- Learn from your mistakes.
- Don’t just take from the community, always give back.
I hope that I was able to help and deliver good resources for the newbies in bug bounty and for those who want to know my methodology and my perspective about bug bounty.
Year over year bug bounty is getting harder, but it doesn’t mean that you can’t start. Go ahead and start learning if you want to be a great hacker :)
I still consider myself a beginner who have a lot to learn on the contrary of where most people see me. Yes I have great achievements that I am really proud of, but I am here to learn as well :)
I appreciate all who post good stuff and share knowledge in bug bounty community and I appreciate your time reading this.
Hope this article will help you get better and give you new knowledge.
Ahmad Halabi.
You can reach me via:
Kind Regards.

